A Deep Dive into Windows Hello (2) - Hackers In inTrusion Laboratory
4.9 (368) · € 16.00 · En Stock
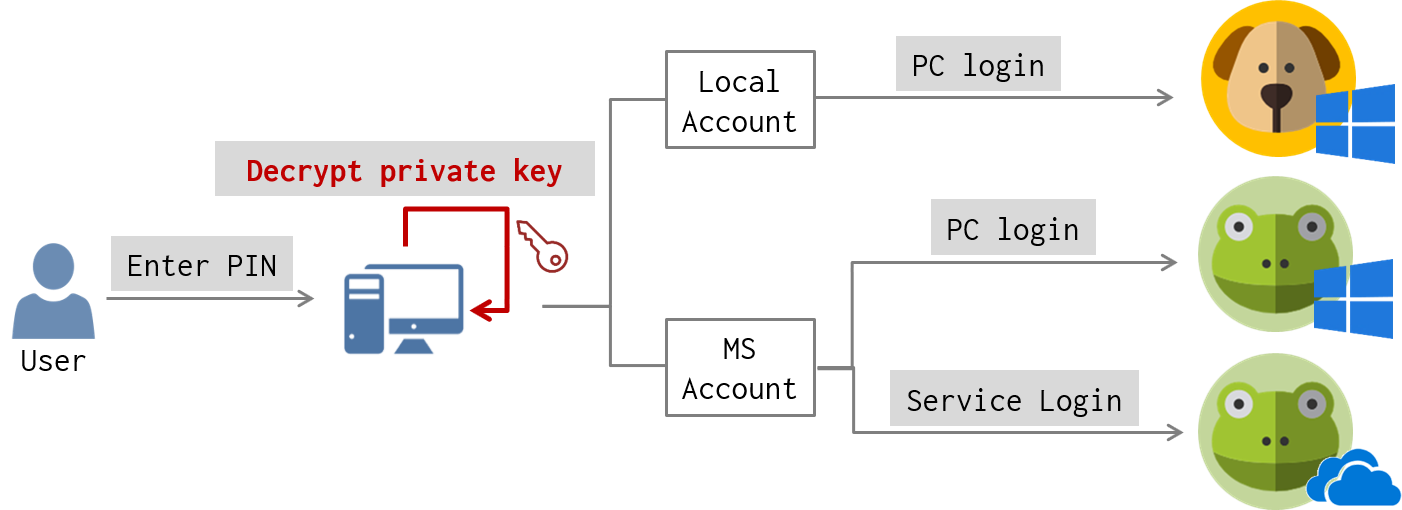
Client-side Login Procedures With protocol analysis, we figure out what data is exchanged between the client and the server for Windows Hello login. Now we’d like to know where is authentication data stored in the client-side? And how authentication data is used to? For these, we performed static and dynamic debugging for login-related services on … Continue reading A Deep Dive into Windows Hello (2) →
New 0-Day Attack Targeting Windows Users With Microsoft Offi - vulnerability database

ULTIMATE HACKER SUMMER CAMP — Part Five: DEFCON Safe Mode, by DCG 201

Future Internet, Free Full-Text

Researchers Find Vulnerability in Windows Hello

Virtual Security Lab Setup - OWASP Broken Web Apps, Webgoat, & ZAP
/cdn.vox-cdn.com/uploads/chorus_asset/file/25104383/windowshellofingerprint.jpg)
Microsoft's Windows Hello fingerprint authentication has been bypassed - The Verge

The Art of Invisibility: The World's Most Famous Hacker Teaches You How to Be Safe in the Age of Big Brother and Big Data: Mitnick, Kevin, Vamosi, Robert, Hypponen, Mikko: 9780316380508:
TuxCare Blog - Insights and News on Linux Technology
The Hacked World Order Council on Foreign Relations

Improve threat detection with hids and alien vault usm

Game of Tokens: AD post exploitation with Token Impersonation, by Jinendar Kothari
Abusing P2P to Hack 3 Million Cameras - TIB AV-Portal